top of page
Search


A Small Business Roadmap for Implementing Zero-Trust Architecture
Most small businesses aren’t breached because they have no security at all. They’re breached because a single stolen password becomes a master key to everything else. That’s the flaw in the old “castle-and-moat” model. Once someone gets past the perimeter, they can often move through the environment with far fewer restrictions than they should. And today, with cloud apps, remote work, shared links, and BYOD, the “perimeter” isn’t even a clearly defined boundary anymore. Zero-
4 min read


The 2026 Guide to Uncovering Unsanctioned Cloud Apps
If you want to uncover unsanctioned cloud apps, don’t begin with a policy. Start with your browser history. The cloud environment most businesses actually use rarely matches the one shown on the IT diagram. It’s built through countless small shortcuts: a “just this once” file share, a free tool that solves one problem faster, a plug-in installed to meet a deadline, or an AI feature quietly enabled inside an app you already pay for. In the moment, none of it feels like a probl
4 min read


OWL360IT is Now an Official Alarm.com Partner
Smarter Intrusion Protection & 24/7 Monitoring for Your Business At OWL360IT , we’re excited to announce that we are now an official partner of Alarm.com , expanding our security offerings to include advanced intrusion detection systems and professional monitoring services . As cyber threats continue to evolve, physical security is just as critical. Our partnership with Alarm.com allows us to deliver a fully integrated security solution —combining IT, cybersecurity, and phys
2 min read

OWL360IT is Now an Official Rogers Business Partner
We’re excited to announce that OWL360IT is now an official partner with Rogers Communications . This partnership allows us to expand our service offerings and provide our clients with direct access to enterprise-grade connectivity solutions , all backed by one of Canada’s largest and most reliable networks. What This Means for Our Clients As a Rogers partner, we can now quote, provision, and support a full range of business communication services, including: 🔌 Business Inte
2 min read

How to Run a "Shadow AI" Audit Without Slowing Down Your Team
It usually starts small. Someone uses an AI tool to refine a difficult email. Someone enables an AI add-on inside a SaaS app because it promises to save an hour a week. Someone pastes a paragraph into a chatbot to “make it sound better.” Then it becomes routine. And once it’s routine, it stops being a simple tool decision and becomes a data governance issue: what’s being shared, where it’s going, and whether you could prove what happened if something goes wrong. That’s the co
4 min read
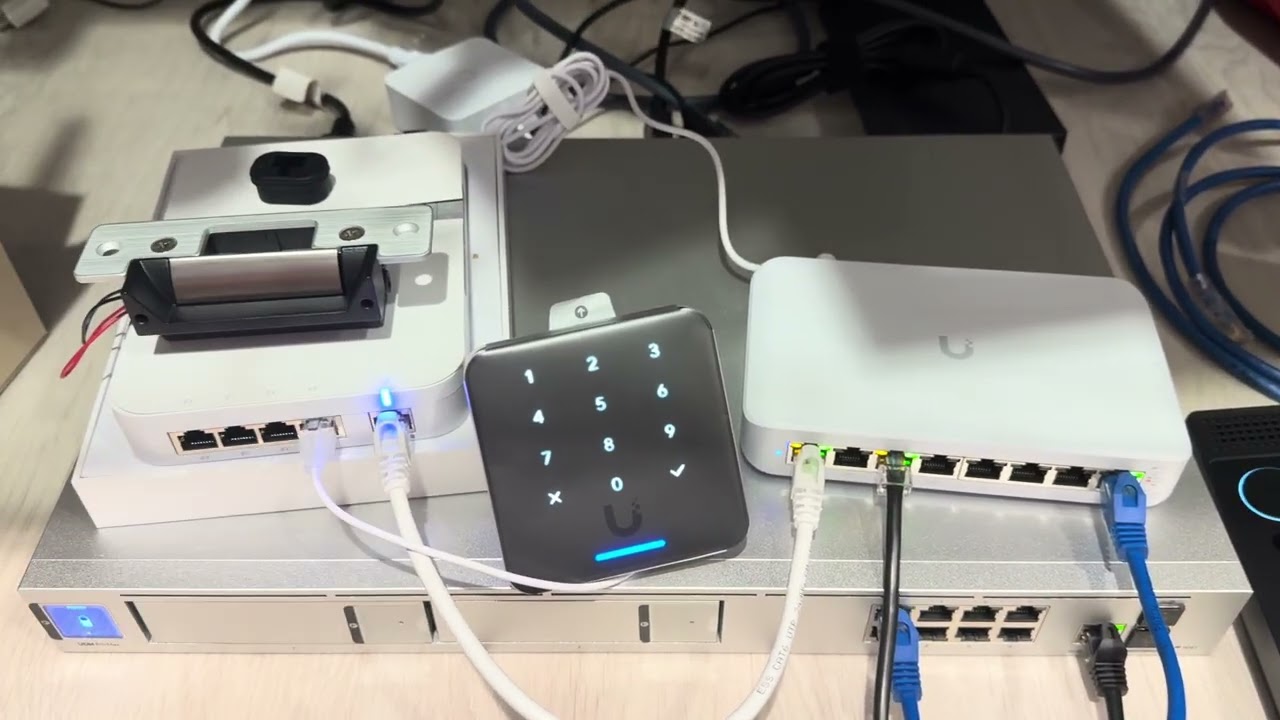
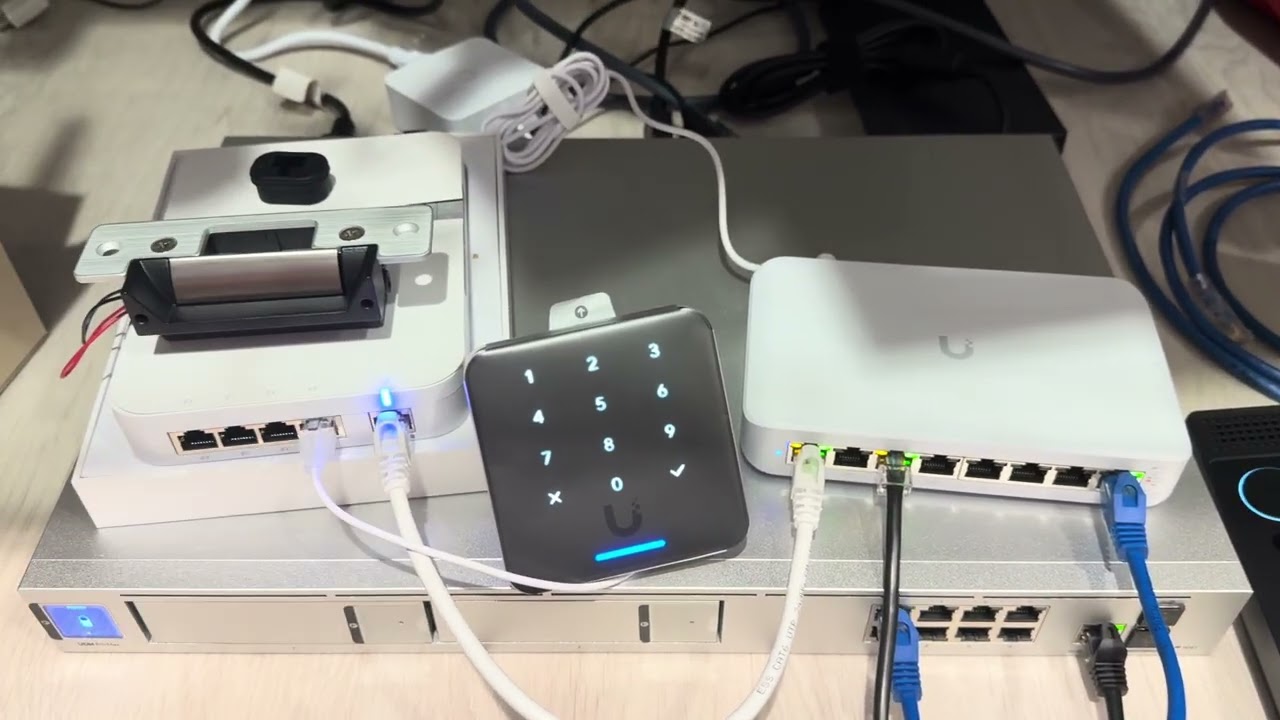
Building a Modern Access Control Lab with UniFi (Mag Locks, NFC & G6 Entry Camera)
Access control has traditionally been complex, expensive, and fragmented across multiple systems. With UniFi Access, that’s starting to change. In this lab setup, I wanted to test a clean, modern approach to door access using the UniFi ecosystem — combining a magnetic door strike, NFC reader, and the new G6 Entry camera into a single, unified platform. Why UniFi for Access Control? One of the biggest challenges with traditional access systems is integration. You often end up
2 min read


5 Security Layers Your MSP Is Likely Missing (and How to Add Them)
Most small businesses aren’t falling short because they don’t care. They’re falling short because they didn’t build their security strategy as one coordinated system. They added tools over time to solve immediate problems, a new threat here, a client request there. On paper, that can look like strong coverage. In reality, it often creates a patchwork of products that don’t fully work together. Some areas overlap. Others get overlooked. And when security isn’t intentionally de
4 min read


The Essential Checklist for Securing Company Laptops at Home
At home, security incidents don’t look like dramatic movie hacks. They look like stepping away from your laptop during a delivery, or leaving it unlocked while you grab something from another room. Those ordinary moments, repeated over time, are how work devices end up exposed. A remote work security checklist focuses on simple, practical controls that hold up in real life. Put it in place once, make it routine, and you’ll prevent the kinds of issues that hurt most because th
4 min read


Stop Ransomware in Its Tracks: A 5-Step Proactive Defense Plan
Ransomware isn’t a jump scare. It’s a slow build. In many cases, it begins days, or even weeks, before encryption, with something mundane, like a login that never should have succeeded. That’s why an effective ransomware defense plan is about more than deploying anti-malware. It’s about preventing unauthorized access from gaining traction. Here’s a five-step approach you can implement across your small-business environment without turning security into a daily obstacle course
4 min read


Zero-Trust for Small Business: No Longer Just for Tech Giants
Think about your office building. You probably have a locked front door, security staff, and maybe even biometric checks. But once someone is inside, can they wander into the supply closet, the file room, or the CFO’s office? In a traditional network, digital access works the same way, a single login often grants broad access to everything. The Zero Trust security model challenges this approach, treating trust itself as a vulnerability. For years, Zero Trust seemed too comple
4 min read


Installing a UniFi G6 Turret with the Camera Arm Mount Bracket
The UniFi (Ubiquiti) G6 Turret is a compact, high‑resolution camera that fits well in both residential and commercial deployments. When paired with the UniFi camera arm mount bracket, it becomes an especially clean solution for wall‑mounted exterior installs where conduit, brick, or block construction would otherwise make cable management difficult. This post walks through a real‑world installation on a concrete block exterior wall, highlighting cable routing, weatherproofing
3 min read


The Supply Chain Trap: Why Your Vendors Are Your Biggest Security Risk
You invested in a great firewall, trained your team on phishing, and now you feel secure. But what about your accounting firm’s security? Your cloud hosting provider? The SaaS tool your marketing team loves? Each vendor is a digital door into your business. If they leave it unlocked, you are also vulnerable. This is the supply chain cybersecurity trap. Sophisticated hackers know it is easier to breach a small, less-secure vendor than a fortified big corporate target. They kno
4 min read


The 2026 Hybrid Strategy: Why “Cloud-Only” Might Be a Mistake
Since cloud computing became mainstream, promising agility, simplicity, offloaded maintenance, and scalability, the message was clear: “Move everything to the cloud.” But once the initial migration wave settled, the challenges became apparent. Some workloads thrive in the cloud, while others become more complex, slower, or more expensive. The smart strategy for 2026 is a pragmatic hybrid cloud approach. A hybrid cloud strategy blends public cloud services like AWS, Azure, an
3 min read


The “Insider Threat” You Overlooked: Proper Employee Offboarding
Imagine a former employee, maybe someone who didn’t leave on the best terms. Their login still works, their company email still forwards messages, and they can still access the project management tool, cloud storage, and customer database. This isn’t a hypothetical scenario; it’s a daily reality for many small businesses that treat offboarding as an afterthought. Many businesses don’t realize how much access departing employees still have. When someone leaves, every account,
4 min read


Managing Cloud Waste as You Scale
When you first move your data and computing resources to the cloud, the bills often seem manageable. But as your business grows, a worrying trend can appear. Your cloud expenses start climbing faster than your revenue. This is not just normal growth, it is a phenomenon called cloud waste, the hidden drain on your budget hiding in your monthly cloud invoice. Cloud waste happens when you spend money on resources that do not add value to your business. Examples include underuse
4 min read


Beyond Chatbots: Preparing Your Small Business for “Agentic AI” in 2026
AI chatbots can answer questions. But now picture an AI that goes further, updating your CRM, booking appointments, and sending emails automatically. This isn’t some far-off future. It’s where things are headed in 2026 and beyond, as AI shifts from reactive tools to proactive, autonomous agents. This next wave of AI is called “Agentic AI.” It describes AI that can set a goal, figure out the steps, use the right tools, and get the job done on its own. For a small business, tha
4 min read


Securing the ‘Third Place’ Office Policy Guidelines for Employees Working From Coffee Shops and Coworking Spaces
The modern office extends far beyond traditional cubicles or open-plan spaces. Since the concept of remote work became popularized in the COVID and post-COVID era, employees now find themselves working from their homes, libraries, bustling coffee shops, and even vacation destinations. These environments, often called “third places,” offer flexibility and convenience but can also introduce risks to company IT systems. With remote work now a permanent reality, businesses must
4 min read


The Server Refresh Deadline: Why Windows Server 2016’s End of Support Should Drive Your Cloud Migration Plan
Time moves fast in the world of technology, and operating systems that once felt cutting-edge are becoming obsolete. With Microsoft having set the deadline for Windows Server 2016 End of Support to January 12, 2027 , the clock is ticking for businesses that use this operating system. Once support ends, Microsoft will no longer provide security updates or patches, leaving your business systems vulnerable. It’s not just about missing new features, continuing to use unsupported
4 min read


Owl360IT Provides Ongoing IT Support for Flamingo Car Wash Systems in London, ON
Owl360IT provides ongoing PC and IT support for the operational systems at Flamingo Car Wash , helping ensure the car wash’s technology runs reliably, securely, and efficiently every day. Flamingo Car Wash relies on multiple integrated PC-based systems to manage wash operations, payment processing, license plate recognition, and membership access. Owl 360 IT supports these systems through proactive monitoring, troubleshooting, and maintenance minimizing downtime and keeping c
1 min read


The MFA Level-Up: Why SMS Codes Are No Longer Enough (and What to Use Instead)
For years, enabling Multi-Factor Authentication (MFA) has been a cornerstone of account and device security. While MFA remains essential, the threat landscape has evolved, making some older methods less effective. The most common form of MFA, four- or six-digit codes sent via SMS, is convenient and familiar, and it’s certainly better than relying on passwords alone. However, SMS is an outdated technology, and cybercriminals have developed reliable ways to bypass it. For organ
4 min read
bottom of page
